
Duplicate unprotected Mifare Classic NFC Card
Where I live, they have changed the way they pickup garbage. Only plastic, paper, and green-stuff will be picked up (in separate bins). And the ordinary (formerly grey) trash you need to bring to one of the central bins in the neighborhood (and glass you have to bring to the bins at the shopping mall).
So, those central “grey” bins… to prevent just anyone from dropping stuff in there, you need to use an RFID badge to open it up. I thought it was a nice challenge to see if I could use a key-chain hanger tag instead of the card to open the bin. So I went ahead and did some searching…
It turned out this was actually almost too easy to write a blog post about. Too many people have been there before. Oh well, then just a small post with the hardware, tools, and commands I had to use. This will serve nicely as a search (or memory) starting point in case I like to create some more copies later on.
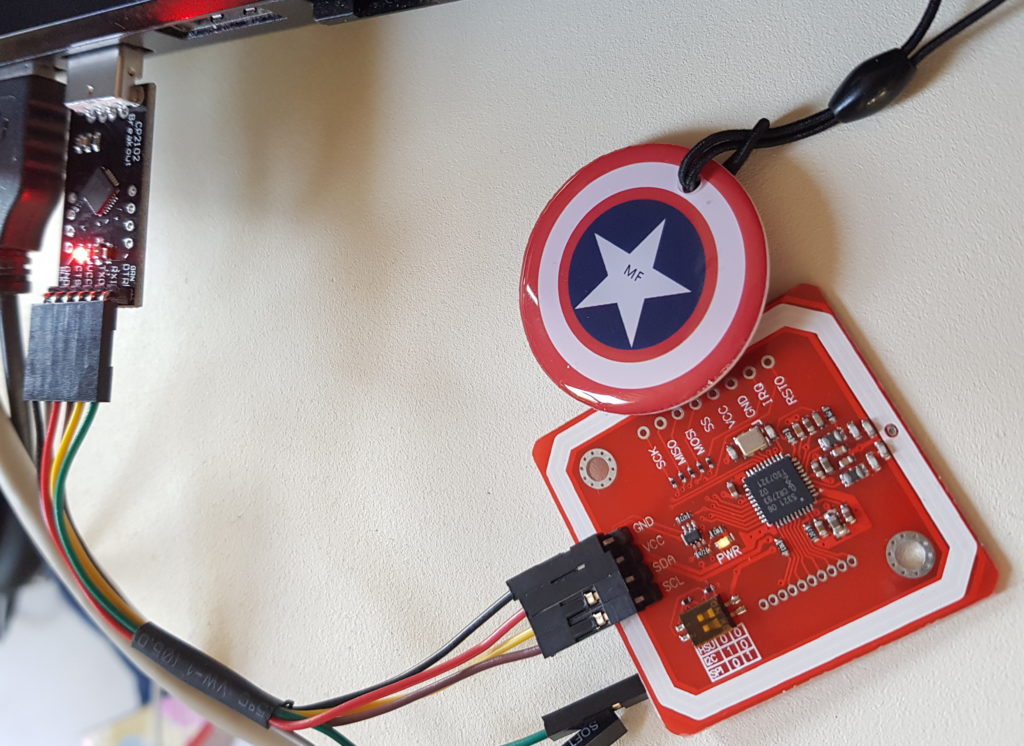
For the hardware, I used a USB to Serial adapter, and a PN532 NFC RFID module which has a serial port. The card and key-chain tag which came with that were of no use. It seemed I had to order a special one, which allows it’s UID to be rewritten.
The software; mfoc and nfc-mfclassic. Two command line tools, usable with Ubuntu Linux.
Connecting the hardware together was easy; just connect GND and VCC of the USB/Serial to the RFID module. And connect the TXD and RXD crossed over to the RXD and TXD (the read of the one connected to the transmit of the other, and vise-versa).
And then run the tools;
# read (unprotected!) source card
mfoc -P 500 -O backup.dmp
# read (default) keys from destination card
mfoc -P 500 -O empty.dmp
# and try writing data using both images
nfc-mfclassic W A backup.dmp empty.dmpCode language: PHP (php)Thats it… copy done. Note: this only works with unprotected (or protected using standard keys) Mifare Classic cards. If the card issuer uses it like this, I’m assuming they do not mind for us to create a “backup” card. Otherwise they would have gone for non-standard keys, or the more complex not-yet-hackable follow up of the classic card. That one uses complex certificate stuff for encrypted storage. If you do encounter a Mifare Classic which does not use the standard keys, you could search for a tool called mfcuk. It might be able to recover the key (not tested, the card was standard).
Thijs.

Product titles used (to help you find the items):
- UID Changeable NFC IC Tag Rfid Keyfob Token 1k S50 13.56MHz Writable ISO14443A
- (10PCS) 13.56 Mhz RFID M1 S50 UID Changeable Card Tag Keychain Key Keyfob ISO14443A Block 0 Sector Writable
- 1Set GREATZT PN532 NFC RFID Wireless Module V3 User Kits Reader Writer Mode IC S50 Card PCB Attenna I2C IIC SPI HSU For Arduino
Oh, and for anyone zooming in to the article image. Yes, it seems like the USB/Serial is connected to SDA/SCL… but it’s not 😉 The back side of the module mentions TX and RX for those same pins, and the dip-switch is configured for serial use. The module can also be switched to I2C or SPI if needed.