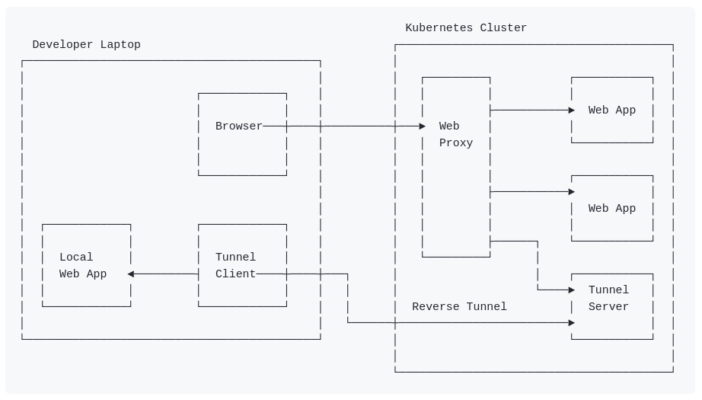
DevTunnel – A Reverse Proxy Tunnel
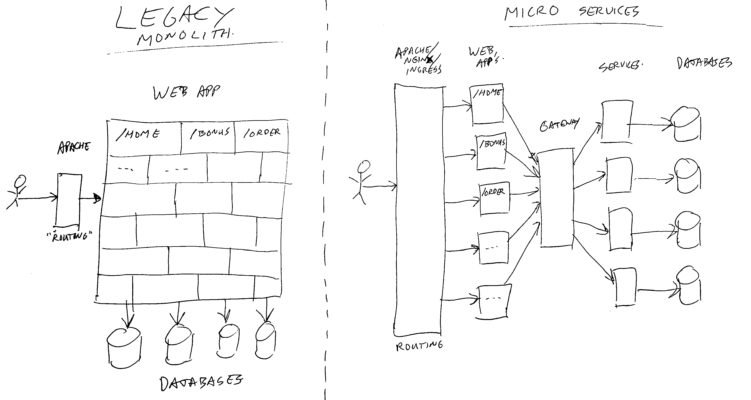
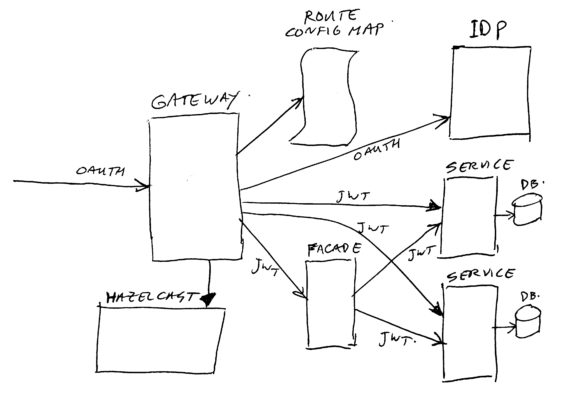
I wanted to have the option to run a web-application on my local machine, and make it seem as if it is running as part of a collection of web-applications on a remote cluster. The collection of web-applications on the cluster make up the whole of a web-site, and during development you might want to “replace” one of the web-app’s by a version on your own machine, which is under development. Note: where this story mentions web-app or web-proxy, you…